
Welcome to Marsh Commercial – your local insurance broker.
Just ask Mike at Correll Group who were looking to address restrictions in moving vehicles back and forth across Europe. Needing support with insuring activities in foreign markets whilst also driving internal efficiencies by consolidating multiple insurance policies into a single point of contact. Up stepped local expert Mark from our Newcastle office...
Harnessing the winds of opportunity for Correll Group
What insurance do you need?
Not sure what insurance you need?
That's okay, many of our clients felt the same. Our friendly team of experts are on hand to help you.
Why choose us?
We go the extra mile to help you understand your unique risks. Don’t just take our word for it, see how Ray and Tim from our Birmingham office helped GCL Food Ingredients understand what current insurance they had, and what they needed. Read more here.
At a glance:
- 8+ years - the average our clients stay with us, not bad considering there's 165,000 of them.
- 45+ local UK offices - from Newquay to Elgin or Cardiff to Witham, we’ve got you covered.
- £26,900 donated to your local heroes - as part of our For the People Awards 2022.
- 150+ years heritage - as part of Marsh McLennan.
- In house claims team - alongside consultants guiding you should you ever need to make a claim.
"What sets Marsh Commercial aside from other insurance companies and brokers is the people."
- Andrew Stott, ICAEW
Have we met before?
Bluefin, Clark Thomson, Jelf - our history as a local UK insurance broker goes back a long way.
In 2015 Jelf became part of Marsh, joining the Marsh McLennan (MMC) family of businesses. MMC are the world's leading professional services firm in risk, strategy and people, helping clients survive and grow in changing times for over 150 years.
A year later (2016), Bluefin merged with Jelf. 2018 saw Clark Thomson welcomed to the family with open arms. And in 2020 these brands evolved to become Marsh Commercial.
Today, our business is structured to deliver the power of Marsh right on your doorstep. While part of a world-leading insurance group, we’re proud to be a UK community broker specialising in servicing SME businesses, across a local branch network the length of the country. That makes us big enough to keep you safe, but small enough to care.
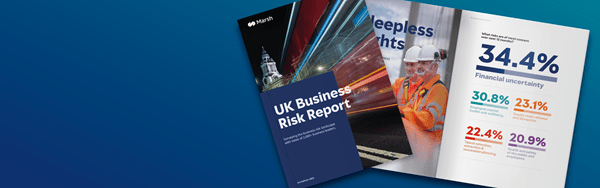
What’s putting you at risk?
What business insurance do I legally require?
The insurance you legally require may depend on a variety of factors such as the nature of your business, the number of employees you have, and the type of work you do. Some of the most common types of insurance that SMEs in the UK typically need include:
- Employers liability insurance: This is a legal requirement for businesses with one or more employees. It covers the cost of compensation claims made by employees who are injured or become ill as a result of their work.
- Public liability insurance: This is not a legal requirement, but it is recommended for businesses that interact with members of the public. It covers the cost of compensation claims made by members of the public who are injured or have their property damaged as a result of your business activities. It may be a contractual requirement depending on the industry you work in.
- Professional indemnity insurance: This is recommended for businesses that provide professional services, such as accountants, architects, or solicitors. It covers the cost of compensation claims made by clients who suffer financial loss as a result of your professional advice or services. It may be a contractual requirement depending on the industry you work in.
- Business property insurance: This covers damage to your business premises, equipment, and stock caused by events such as fire, theft, or flooding.
Not sure what insurance you need?
That's okay, many of our clients felt the same. Our friendly team of experts are on hand to help you.
Frequently asked questions
Whether you’re a sole trader, independent or growing corporate - no matter your size or what you do, we can help protect you with right the business insurance.
We can also help protect your boats through our Bishop Skinner Marine brand, your boilers through BoilerPlus, and can arrange specialist insurance policies for talking therapists under our well-known Oxygen brand.
Your family, assets and lifestyle are also equally important to us – learn more about our Private Clients insurance team.
Yes - our commercial property owners insurance has been specially designed so that your properties are protected under one policy. If you own several commercial properties, we may be able to save you time and money. There’s no need to juggle multiple policies with us on your side.
Yes – we can arrange the right commercial combined insurance for your business from our panel of the UK’s leading and specialist insurers.
Get covered for property damage, business interruption, employers liability, public liability, personal accident cover, money and goods in transit – under one simple policy.
Yes – get protected with the right landlord insurance from our selection of the UK’s leading and specialist insurers.
Yes – we can arrange the right insurance from our selection of the UK’s leading and specialist insurers to help you get your stock and contents covered.
Marsh is our parent company and is the leader in insurance broking and risk management. They’re a part of the Marsh McLennan (MMC) family of businesses, and help corporate clients quantify and manage risk – and unlock new possibilities for growth.
Click here to access your Marsh Commercial client portal where you can manage your policy, view your documents, and make payments online.
Not set yours up yet? That’s ok, simply contact your Marsh Commercial adviser who will be able to help.
The first step in the event of any claim is to let us know about it. Please contact your Marsh Commercial adviser who will then put you in touch with your dedicated claims adviser. Alternatively contact us on 0330 818 7677 or get in touch here.
We’re sorry you’ve been unable to locate your renewal documents. The quickest way to see what’s happened is to contact your local office. If you are unsure which office you need to contact, please get in touch here.








